Most of us have heard of ‘phishing’ and how it is a scam to send you fake emails to trick you into giving up some personal information, such as passwords or banking details. Since the term is ‘nothing new’ we tend to tune this out and think that we will never fall for this old trick. However, evidence shows that phishing is becoming a more common and increasing threat. As attackers are more sophisticated in their approach, both businesses and users face great security risk. Even with proper security training in place, identifying and fending against phishing requires both users and enterprises to step up their security vigilance.
What Is Phishing And Why We Have To Be Concerned Today
Phishing is the fraudulent practice of contacting the target per email, phone or message by someone posing as a legitimate institution to induce individuals to reveal sensitive information, such as passwords or banking and credit card details. It remains the method-of-choice for most cybercriminals to access users’ online accounts and data, infect computers, and extract sensitive information. As a form of hybrid cyber attacking it combines both social engineering and technological aspects to target users. Social engineering is the art of tricking users to give up confidential information, open malicious links, launch dangerous files, or to send money directly to the attacker.
Despite phishing being quite an old method for security attacks, it continues to be popular due to its simplicity and effectiveness. The reason is because it manages to target the weakest link in the security chain: the user. Since the attacker is usually disguised as a trustworthy entity, users are often unaware of the trap they fall into. Most likely that is the reason for why phishing accounts for a whopping 90% of all data breaches. Phishing has become even more relevant as it has lately increased exponentially, today growing by 12 times more compared to just five years ago. The main driver for this is the COVID pandemic that saw a shift to online services as people become more integrated into the digital world. As a result, a 2021 cybersecurity study found that 86% of organizations across industries had at least one user being led to a phishing site. Similarly, 70% of organizations had users that were served malicious browser ads.
Methods And Formats Of Phishing Attacks
Although phishing began in the form of emails, it has by now evolved into various sophisticated formats. Today, phishing can happen via any type of user interaction, such as an email, SMS (smishing), instant message, social networking sites like Facebook, phone calls, message boards, banner ads, websites, voice messages, or even multiplayer games. The attack leads the user to a deceptive domain name which appears trustworthy and legitimate but is in fact controlled by the attacker. Exploiting human factors such as curiosity, fear, and empathy, the user is made comfortable to click the link, and enter passwords or personal information.
The attackers are often highly skilled in technical understanding of computer communications, and they understand security protocols and common casual habits of users. Using this knowledge, they find methods to bypass security protocols (whether it being technological or human processes) and evade detection, increasing the chances of a successful attack. The frequency and diversity of attacks targeted at users also helps the chances of a successful attack. In a study on phishing from the International Journal of Security and its Applications, even well-trained users failed to detect 29% of phishing attacks.
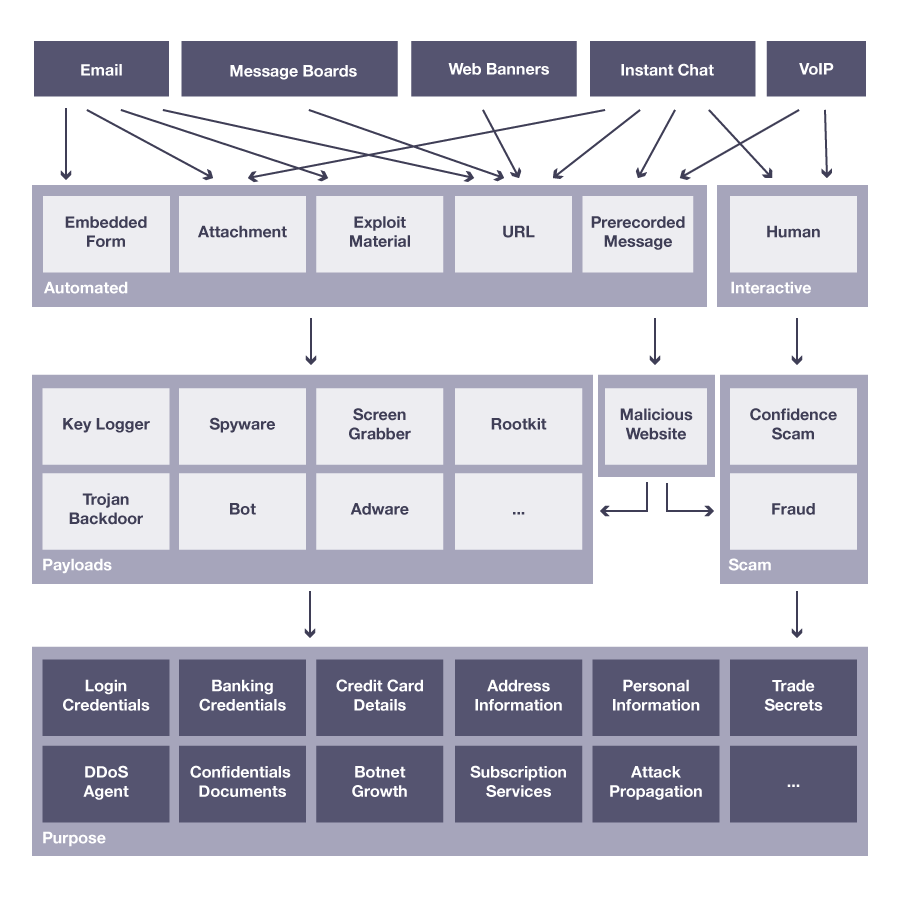
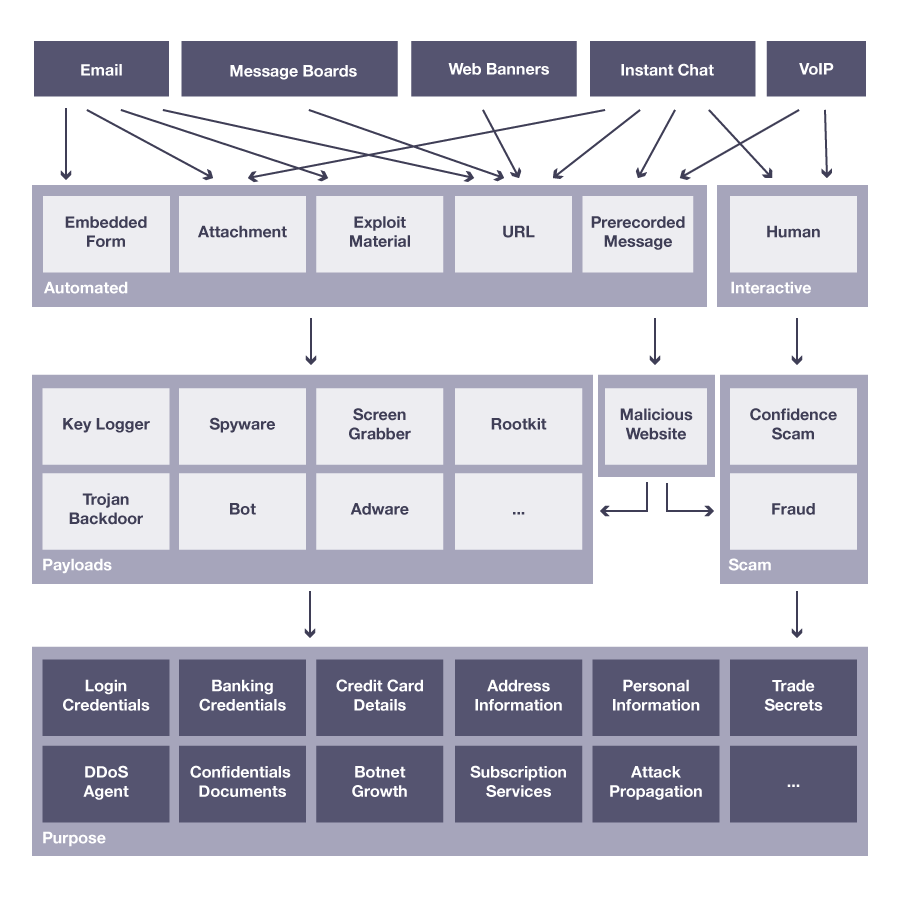
Below, you can see an illustration of the methods used in phishing, including various communication channels and purposes for phishing:
Why Do Phishing Attacks Succeed?
Phishing attacks disguise themselves as trustworthy entities, and rely on reputation and human level relationships with the target to discover sensitive information. Because phishing is even more a social science problem than a technological one, attackers leverage social engineering tools to capitalize on victims. A phishing attack commonly contains three key components: lure, hook, and catch.
- Lure: a communication (like an email) that appears to be from a trustworthy and legitimate source (like a bank or internet service provider). The lure contains a link or attachment to the hook, often hidden by obscuring the fake link.
- Hook: a website or platform that mimics the site of the trustworthy entity which the victim is willing to share confidential information to (like an e-banking website).
- Catch: the attacker makes use of the information that the victim willingly shares to the trusted entity.
Social engineering attacks succeed because they exploit the curiosity, fear, and empathy factors of humans.
- Curiosity: the desire to stay informed, such as sharing a link to watch a video about the latest news stories. The destination link then leads the user to a malicious site.
- Fear: to persuade the users in a certain way by instilling fear or urgency. For example, encouraging users to validate themselves because their account may be breached, causing the user to share personal information on a malicious site.
- Empathy: towards others, by touching on human relationships. For example, the attacker could impersonate a friend or relative, or exploit tragedies such as asking the user to donate money to a cause like an earthquake or tsunami.
Finally, phishing attacks will use multiple technical tricks that make the interaction further convincing:
- Trademarks, logos, and images associated with the trustworthy entity.
- Advice to not click links or other warnings against phishing may actually make the communication seem more legitimate, where the user clicks the links anyway.
- Spoofing where the apparent sender of the message is changed, for example, making it look like the communication is coming from your manager or friend.
- URL hiding and encoding.
As a conclusion, a combination of above tactics coupled with high frequency and targeted phishing (also known as spear phishing), attackers raise their chances of success. In addition timing plays a key role as statistics have shown that phishing attacks peak during holiday times, and soar by as much as 52% in December. Despite attackers having high technological skills that they implement in combination with various communication tactics, phishing continues to leverage on the weakest link, being the user.
How Can I Best Detect And Avoid A Phishing Attack
Detecting a phishing attempt can be difficult as the attackers are often skilled in creating a sense of urgency or importance that causes the victim to act before processing the request.
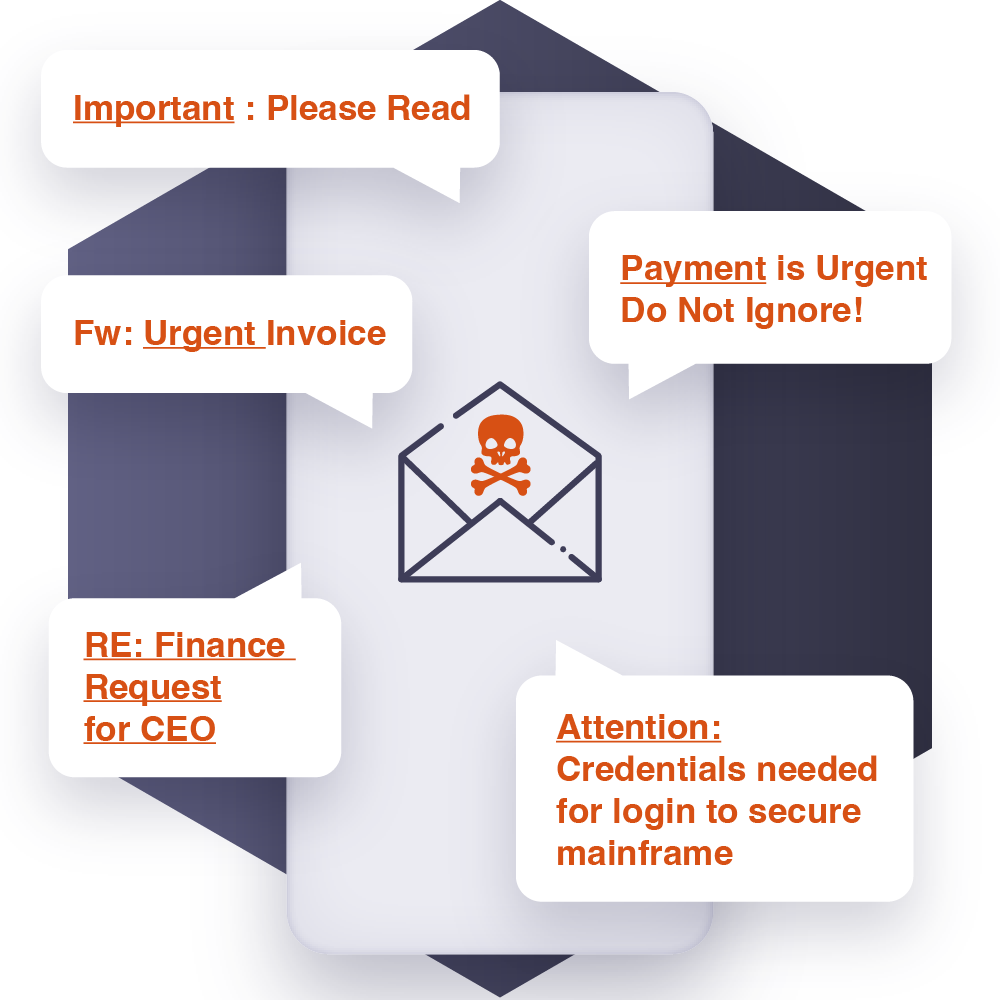
Look out for emails, SMS, messages or any forms of communication that include the words Urgent (8.0% of top phishing email keywords), Request (5.8%), Important (5.4%), Payment (5.2%), and Attention (4.4%). Additionally, the most common themes include Bill (15.7% of phishing emails), Email delivery failure (13.3%), and Package delivery (2.4%).
The most typical subject lines in 2020 included social media or security upgrade requests:
| IT: Annual Asset Inventory | Medical: Changes to your health benefits | Twitter: Security alert: new or unusual Twitter login |
| Amazon: Action Required: Your Amazon Prime Membership has been declined | Zoom: Scheduled Meeting Error | Google Pay: Payment sent |
| Financial: Stimulus Cancellation Request Approved | Microsoft 365: Action needed: update the address for your Xbox Game Pass for Console subscription | Workday: Reminder: Important Security Upgrade Required |
Steps To Take When You Receive A Suspicious Or Urgent Message:
- Take a minute to think before you take action
- Do not click odd links or open suspicious attachments
- Check the email address for strange spelling or characters
- Look for spelling or grammar mistakes
- Watch out for poor formatting
- Reach out to the sender through a different channel if you are not sure whether the message is real
What Should I Do If I Identify A Phishing Attack?
Once you have identified the communication to be an attack:
- Do not click on any links!
- Do not reply or forward the communication!
- Do not open attachments!
- Report and alert your IT Security Team or management
- Otherwise, consider to report the phish to Google Safe Browsing
If you are an enterprise and you want to increase your security against phishing attacks then check out how and why Gartner recommends FIDO2 authentication as an anti-phishing solution here.
Learn more about Futurae’s FIDO2 solutions, or other fraud detection methods. If you have questions or feedback, please let us know.